Ending Zero-Sum Games: In-Depth Research Report on Web3 Incentive Engineering and Odyssey Behavioral Dynamics
1. Prologue – The “Singularity” of Odyssey
1.1 Paradigm Shift: Why Do Most Project Odysseys Yield Minimal Results?
Although the Odyssey model has created many wealth-creation myths, as we enter 2026, developers are finding it increasingly difficult to generate “breakout effects” by simply imitating leading projects. This lack of efficacy is fundamentally due to a deep fracture between incentive logic and user ecosystems.
- Incentive entropy increase has triggered severe homogenized involution.
When 90% of projects in the market require users to repeat “cross-chain, staking, and sharing” actions to earn nearly identical “Points,” the marginal return on user attention plummets. This model imitation leads to incentive entropy increase—the scarcity of rewards is diluted by a flood of homogeneous projects. Taking Linea’s “The Surge” and the subsequent wave of L2 points wars as examples, when users find they need to move liquidity across dozens of protocols with highly similar logic for diminishing, inflationary points, aesthetic fatigue evolves into behavioral “lying flat.” The incentive effect is exhausted in endless involution.
- The lack of game-theoretic mechanisms creates “Sybil-style growth,” producing massive false prosperity.
Many projects only learn the superficial “task wall” but neglect the deeper anti-Sybil game theory, resulting in most incentives being siphoned off by automated scripts (Farmers) from professional studios. The experience of zkSync Era serves as a classic warning: despite having over 6 million active addresses on paper, deeper data analysis reveals the vast majority were mechanical interactions created for farming airdrops. This “paper prosperity” not only triggered a massive community governance crisis during the TGE phase but, more fatally, saw 90% of addresses rapidly drop to zero after the airdrop distribution. Beyond paying high customer acquisition costs, the project gained no real ecosystem stickiness.
- The “disconnect” between product logic and incentive interactions makes participation mechanical.
Breakout effects often stem from the deep coupling of a product’s core functionality with its reward mechanism. If Odyssey tasks become “on-chain drudgery” unrelated to product value (e.g., requiring privacy protocol users to publicly shill on Twitter), users cannot develop brand affinity. Just like early DeFi projects that forcibly bundled social tasks on platforms like Galxe, they might have gained tens of thousands of followers in the short term, but this “demand mismatch” attracted mostly low-net-worth task hunters. Genuine high-net-worth users were repelled by this Web2-style forced interaction and left. Once the tasks ended, TVL (Total Value Locked) often plummeted within 24 hours, failing to create any emotional resonance or competitive moat.
1.2 Defining Win-Win: Protocol Unit Economics
To break the vicious cycle of “ineffectiveness,” the win-win logic must shift from “buying traffic” to “building an ecosystem.” We need to find the mathematical equilibrium:
1.2.1 Unit Marginal Profit for the Protocol
Projects must recognize that the essence of an Odyssey is the precise allocation of Customer Acquisition Cost (CAC).
Unit Margin = LTVuser – CACincentive
Only when the long-term value a user generates for the protocol—through fees, liquidity stickiness, or governance contributions (i.e., LTV)—exceeds the rewards (Incentive) they receive, does the Odyssey cease to be mere “money burning” and become sustainable capital expansion.
1.2.2 Total Utility Capture for the User
Users in future Odysseys will be more rational. They will no longer settle for “potentially worthless” points but will calculate the comprehensive return rate:
- Airdrop: Immediately realizable token allocation.
- Utility: Long-term protocol rights (e.g., lifetime fee discounts, RWA revenue share).
- Reputation: On-chain credit assets. This is the core credential for accessing future “allowlist whitelists” of top-tier projects.
1.3 Core Hypothesis: Incentives Are Not Just Tokens, But a Composite of Credit, Privileges, and Revenue Rights
In deep incentive design, we completely overturn the old assumption that “ERC-20 tokens are the sole driving force.” An Odyssey capable of achieving a breakout effect must be supported by value across these three dimensions:
- Credit (Credit/Identity)
Permanently solidify user contributions through Soulbound Tokens (SBT) or on-chain identity systems. Credit is not just a badge; it’s a force multiplier: high-credit users can unlock “collateral-free loans” or “task weight bonuses,” giving genuine contributors an advantage over scripts.
- Privileges (Privileges/Utility)
Embed rewards into product usage rights. For example, Odyssey winners could receive a “golden veto right” in protocol governance or “first-mining priority” for other new projects within the ecosystem. Privileges transform users from “passersby” into “long-term stakeholders” of the protocol.
- Revenue Rights (Revenue Rights/RWA)
With the advancement of compliance, the most attractive Odysseys in 2026 are beginning to incorporate underlying dividend logic. Rewards are no longer just inflationary “air,” but are anchored to the protocol’s real revenue (e.g., RWA treasury bond interest, DEX fee sharing). The injection of this real yield is the trump card for projects to stand out amidst bubbles and achieve genuine breakout.
2. User Behavior Spectrum: From “Airdrop Farmers” to “On-chain Citizens”
In the future on-chain ecosystem, the traditional definition of “user” has disintegrated. With the proliferation of full-chain abstraction and AI agents, the souls (or algorithms) behind addresses exhibit extremely high differentiation. Understanding this spectrum is a prerequisite for designing win-win incentive mechanisms.
2.1. User Stratification Model: Deep Profiling Based on Motivation and Contribution
We categorize Odyssey participants into three representative Greek-letter tiers. This stratification is no longer based solely on asset size (TVL) but on behavioral entropy and protocol loyalty.
2.1.1 Player Stratification
Gamma – Arbitrageurs (AI Bounty Hunters)
- Role Definition: AI bounty hunters pursuing extreme efficiency.
- Psychological Drivers: Utterly rational. They have zero interest in project sentiment; their only frame of reference is the “risk-free rate” and “certain returns.”
- Behavioral Manifestation: Typical script-driven interaction with extremely low latency. They appear collectively in gas fee troughs like migratory birds, exhibiting highly standardized and homogeneous behavioral paths.
Beta – Explorers (Hardcore Players)
- Role Definition: Hardcore players deeply engaged with the ecosystem.
- Psychological Drivers: Resonance-driven. They value deep product experience, community identity, and future long-term rights.
- Behavioral Manifestation: Actively participate in deep feature beta testing, taking pride in earning scarce badges (SBTs). They provide high-quality feedback in communities, and their interaction traces carry distinct personal flair and subjective preferences.
Alpha – Builders (Ecological Pillars)
- Role Definition: The foundational support and interest community of the protocol.
- Psychological Drivers: Sovereignty-driven. Their goals are long-term governance rights, dividend rights, and building an impregnable security moat for the protocol.
- Behavioral Manifestation: Manifested as long-term locking of large capital, submitting core code proposals, or running validator nodes. As the text states: “They don’t produce noise; they only produce credit.”
2.1.2 Behavioral Characteristics and Quantitative Models
- Gamma’s Survival Law: Ruthless Cost Estimation
For Gamma players, an Odyssey is a game of precise calculation. They care nothing for the project vision, focusing solely on capital efficiency per unit time.
- Alpha’s Moat Effect: The Game of Power
Alpha players disdain retweeting and liking on Twitter. Their Odyssey is manifested in sovereign contributions. They are the “anchors” of the protocol. The deposit of their large assets and maintenance of technical nodes directly determine the protocol’s market cap ceiling and risk resilience.
2.1.3 Identity Collapse and “Consensus Alchemy”
Identity is not lifelong but a dynamically evolving continuous spectrum. In excellent Odyssey designs, user identity undergoes “quantum leaps”:
- Leap from “Arbitrage” to “Exploration”: A Gamma player initially aiming only to farm might be impressed by the protocol’s exceptional product experience or robust technical logic during deep interaction. When they realize the profit from long-term holding exceeds that from immediate selling, they experience “identity collapse”—transitioning from “farm and dump” to “deep holding.”
- The Project’s “Consensus Capture Power”: This leap is essentially the project’s “alchemy” performed on users. Low-quality projects can only attract and retain arbitrageurs, eventually collapsing as incentives dry up. High-quality projects possess a centripetal force that can transform “bounty hunters” into “forest guardians.”
Core Insight: The incentive mechanism is no longer rigid segregation but a process of screening, filtering, and converting. It acknowledges the existence value of Gammas, but its ultimate mission is to use incentive leverage to induce users to evolve across tiers, from profit-seeking retail to value-aligned partners.
2.2 Behavioral Heatmap Analysis: The Non-linear Nature of Mainstream Layer 2 Task Completion Paths
Before 2024, Odyssey task paths were linear (Step 1: Follow Twitter; Step 2: Bridge; Step 3: Swap). But in the future, “Intent-centric” design will make user behavioral heatmaps exhibit significantly non-linear, network-like characteristics.
2.2.1 Path Divergence from “Task-Driven” to “Intent-Driven”
Through data mining of major L2s like Arbitrum, Optimism, and Base, we find:
- Path Non-determinism: For the same Odyssey task, User A might complete it via “borrow -> stake -> mint,” while User B might achieve it in one click via a “cross-chain aggregator -> auto-strategy pool.”
- Cross-chain Heat Anchors: Behavior is no longer confined to a single chain. User actions on Layer 2 are often accompanied by immediate feedback on associated Layer 3 application-specific chains. For example, 10 minutes after interacting on L2, the heatmap shows users quickly triggering automated yield distribution scripts on a linked AI chain.
2.2.2 Non-uniform Distribution of Behavioral Entropy
Monitoring data shows that high-quality users (Beta and Alpha tiers) have behavioral heatmaps with higher “complexity entropy.”
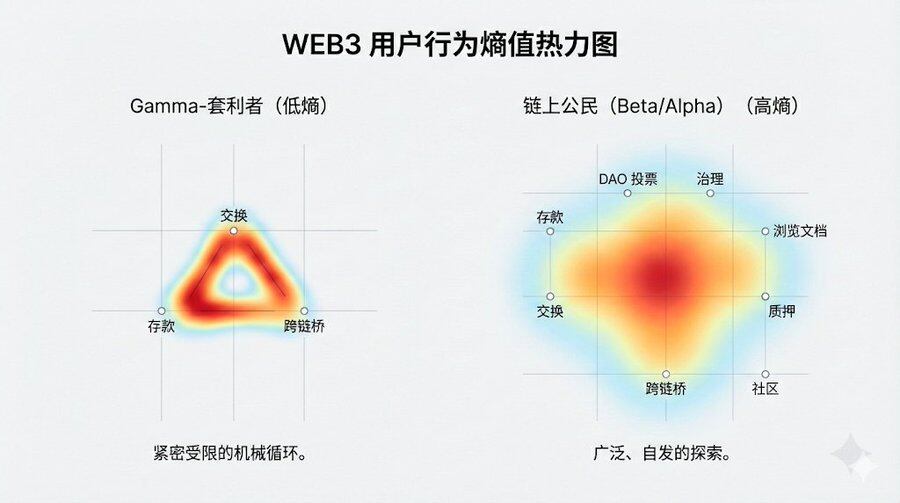
- Gamma-Arbitrageur Heatmap: Exhibits highly mechanical regularity. Interaction points are concentrated within the minimum required task loop, with short and repetitive paths.
- On-chain Citizen Heatmap: Exhibits diffuseness and long-tail characteristics. Beyond completing set Odyssey tasks, they explore secondary protocol pages, read on-chain documentation, or interact with other dApps within the ecosystem.
Insight: The most successful Odyssey projects have heatmaps that are not straight lines but gravitational fields. They attract users to stay within the ecosystem after completing tasks, generating “unplanned” interactions spontaneously.
Users are no longer content to be seen as just a “wallet address.” In Odyssey 3.0, the endpoint of the behavioral spectrum is “on-chain citizenship.” This citizenship signifies not just reward distribution, but an identity endorsement within a multi-chain civilization.
3. Mechanism Design: Mathematical Models and Game-Theoretic Equilibrium for Ensuring “Win-Win”
In the evolution of Web3, early Odysseys were often criticized for falling into the “Ponzi deadlock”: projects traded future inflationary expectations for present false prosperity. To escape this cycle, the core lies in achieving Incentive Compatibility (IC). This means we need rigorous mathematical models to ensure that the path users take to maximize their own interests perfectly aligns with the path for the protocol’s long-term healthy development.
3.1 The Incentive Compatibility (IC) Constraint: Reframing the Game of Cost and Reward
In traditional airdrop models, the marginal cost of Sybil attacks is almost zero. To protect the interests of genuine contributors from dilution, future Odyssey designs introduce IC constraint equations based on game theory.
Core Game-Theoretic Model
Let R(c) be the comprehensive reward an honest user receives for genuine interaction, and C(c) be the hard costs incurred (including gas, slippage, capital opportunity cost, etc.). Simultaneously, let E[R(s)] be the expected reward a Sybil attacker gains by simulating interaction with automated scripts, and C(s) be their attack cost (including servers, IP pools, anti-detection algorithms, and sunk costs from being purged).
The Nash Equilibrium point for achieving win-win must satisfy:
Intervention and Evolution in the 2.0 Era:
- Drastically Increase C(s) (Attack Resistance): Future defense layers no longer rely on simple blacklists but introduce AI behavioral entropy detection. The system analyzes the spatiotemporal distribution of interactions, the correlation entropy of fund flows, and the “human-likeness” of operations. For suspected accounts, the system dynamically applies a “Gas Fee Penalty Coefficient,” forcing them to pay higher transaction fees during non-peak hours, directly destroying the script’s unit profitability.
- Deeply Optimize R(c) (Reward Structure): The reward pool shifts from “pure governance tokens” to a “hybrid rights package.” This includes: Cash Flow Rights: Direct distribution of protocol fee dividends (Real Yield). Privilege Assets: Permanent fee discounts (Gas Rebate) or interest rate boosts for cross-protocol lending. Governance Leverage: Governance weight bonuses for long-term holders, ensuring “genuine participation” yields not just wealth, but power.
3.2 Dynamic Difficulty Adjustment Mechanism (DDA)
Future Odysseys are no longer static task lists. Drawing from Bitcoin’s difficulty adjustment algorithm, advanced protocols are implementing Dynamic Difficulty Adjustment (DDA).
Operational Logic:
When an Odyssey enters an explosive phase, with a sharp increase in total interactive addresses and TVL in a short time, the system automatically senses “overheating.” At this point, the points capture algorithm automatically triggers a difficulty increase:
- Increasing Capital Thresholds: The required interaction amount or liquidity lock-up period to earn equivalent points increases.
- Upgrading Task Complexity: Shifting from simple “one-click Swaps” to “multi-protocol combination strategies” (e.g., borrow on Protocol A, stake on Protocol B, provide hedging on Protocol C).
Win-Win Logic:
- For the Protocol: DDA acts as a safety valve, preventing a sudden influx of speculative traffic from overwhelming liquidity pools and avoiding cliff-like crashes due to “reward exhaustion.”
- For Alpha-Citizens: It protects early, stable builders. High-difficulty tasks naturally filter out unprofessional “farmers,” directing reward shares more precisely to high-net-worth genuine users.
3.3 Proof of Value Model (PoV)
In Odyssey 3.0, “address count” is decisively deemed a Vanity Metric. Projects are fully transitioning to the PoV model, whose core is measuring Contribution Density.
Contribution Density Formula:
We define Contribution Density D as:
D = ∑(Liquidity × Time) + γ × Governance_Activity / Total_Reward
- Liquidity (Capital Stickiness): Measures the “settling duration” of user funds within the ecosystem, not “in-and-out” behavior.
- γ (Community Contribution Factor): A scaling variable. For users actively participating in governance votes, writing technical documentation, or generating genuine positive social network influence, the γ bonus can reach 2x or higher.
- Total Rewards: Acts as the denominator to balance inflation and ensure the value per unit of reward.
Deep Win-Win Analysis:
Through the PoV model, projects no longer receive a list of cold wallet addresses but a genuine map of ecosystem participants. Users discover that, due to the γ factor,
This article is sourced from the internet: Ending Zero-Sum Games: In-Depth Research Report on Web3 Incentive Engineering and Odyssey Behavioral Dynamics
Original Compilation: TechFlow Original Link: In Putin’s Orbit: The Crypto Politics of Jeffrey Epstein and Peter Thiel Introduction: This article reveals how Jeffrey Epstein leveraged his complex international network to push cryptocurrency to the center of geopolitics. Through recently disclosed emails, the article traces the intricate connections between Epstein, Silicon Valley mogul Peter Thiel, former Trump strategist Steve Bannon, and high-level Russian officials. Epstein not only advised Russia to use Bitcoin to ‘leapfrog’ and reshape the financial system but also injected capital into Blockstream at a critical moment to sustain Bitcoin Core development and was deeply involved in Thiel’s venture capital firm. These early crypto-political maneuvers are now, through the rise of figures like J.D. Vance, profoundly influencing global democratic elections and the contest for state power, becoming Epstein’s most…






